Medical Conference Management System India
Conference Management System
We power conference management with smart software that enhances workflow, organization, and operational efficiency.

We power conference management with smart software that enhances workflow, organization, and operational efficiency.


Our Conference Management System goes beyond a simple set of features — it delivers a seamless experience from the first interaction to the final touchpoint. Designed as a highly customizable entrance management solution, it adapts effortlessly to diverse workflows and complex enterprise requirements.
Get a DemoStreamline visitor management with modern, secure, and efficient solutions for your facility.
Access digital visitor logs from anywhere. Cloud records eliminate manual paperwork and storage hassles.
Verify every visitor with automated checks and instant host notifications for enhanced facility safety.
Simple tablet or PC setup enables quick self-service check-ins without complex hardware requirements.
Enable portal-based pre-registration so visitors can schedule and confirm appointments in advance.
Store data securely in the cloud with automated backups and instant access from any device.
Real-time alerts and seamless integrations help staff coordinate visitor interactions efficiently.
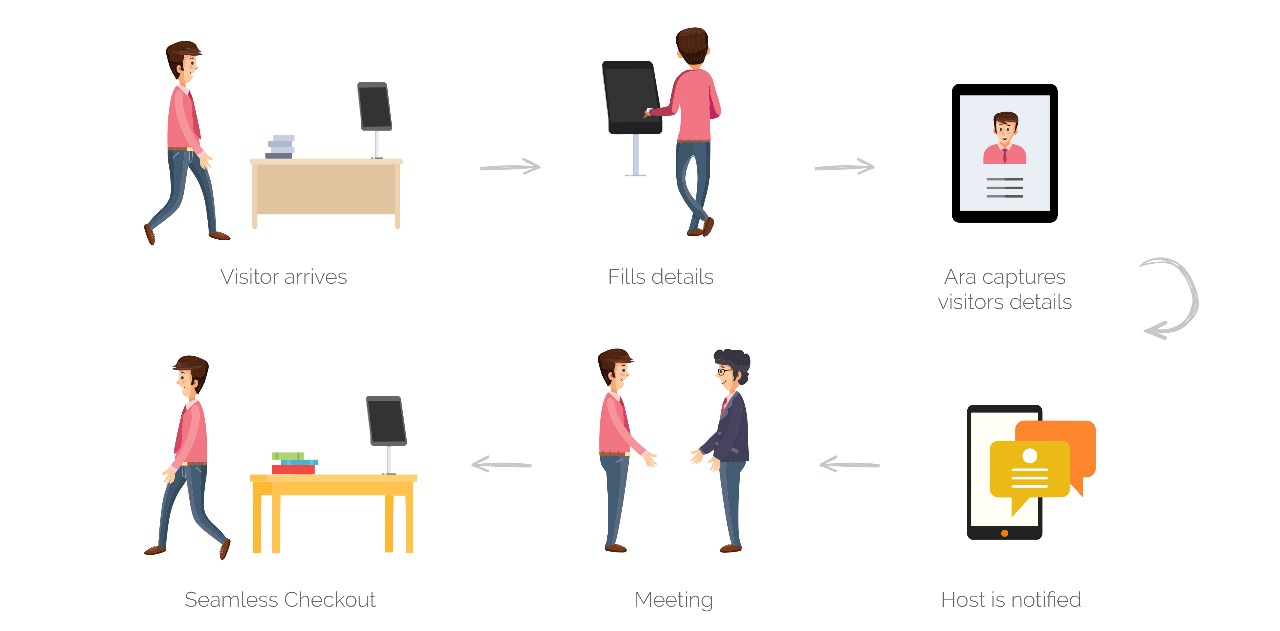












Quickly register a visitor, capture detailed information, print a badge and notify the host. Looking up an existing visitor is as easy. You may look-up a past visitor by a variety of fields such as host, time of visit, etc.
Visitors may be pre-registered through a simple to use web-portal or a smart phone app. Registered visitors receive a notification and are listed in the visitors list for the day.
As visitors are registered or checked-in or checked-out, the system may be configured to send notifications to hosts. The system may also send reminders to visitors as schedule visits approach.

Design your badge in the format and character type you want. Include your company's logo, your guest's name and photo, the date and time of the visit, and any other information you need.
The system keeps track of all visitor actions. This includes all access point entry/exits as well as audit information about check-in/check-outs.
In addition to the standard Visitor Log and Visitor activity reports, many advanced reports may be printed or exported to various formats such as pdf, excel, etc. Reports may be filtered by host, date and time of the visit. Reports may be automatically e-mailed to a pre-configured list of recipients.
Security is a primary focus of the system design. All data communications can be configured to use encryption. In addition to standard security protocols such as HTTPS/SSL, we implement a special multi-phase authentication scheme that makes our systems extremely secure. "Fail-over" and "hot-standby" modules may be used to ensure high availability.
Whether you have a single station visitor reception or a large system with multiple stations spanning across the globe, you use a standard web-browser interface to manage your visitors. No special software required.
The system provides necessary tools to perform security and compliance audits. Complete audit logs are kept for all actions performed by system administrators. Backup and restore capabilities are integral part of the system operation.